Signing your Windows PowerShell scripts will increase security on your system. To achieve this goal, you can use your Trusted Root CA in your Active Directory environment. First, you must change the execution policy to “AllSigned”. Execution policy indicates to PowerShell what can and what cannot be executed on your system.
- Restricted/Default: This is the default policy. You may not launch any script. The only possibility is to use PowerShell in ‘interactive mode’.
- Allsigned: All the scripts that should be executed on the machine must be signed by a ‘Trusted Publisher’.
- RemoteSigned: This concerns only the scripts that have been downloaded from the internet. These scripts must be signed by a ‘Trusted Publisher’.
- Unrestricted: No constraints on the execution of scripts. All the scripts will be executed if you accept a warning message. I do not recommend it in a production environment.
- Bypass: No blockage, no warning message. Everything is executed without control.
- Undefined: Removes the currently assigned execution policy from the current scope. This parameter will not remove an execution policy that is set in a Group Policy scope.
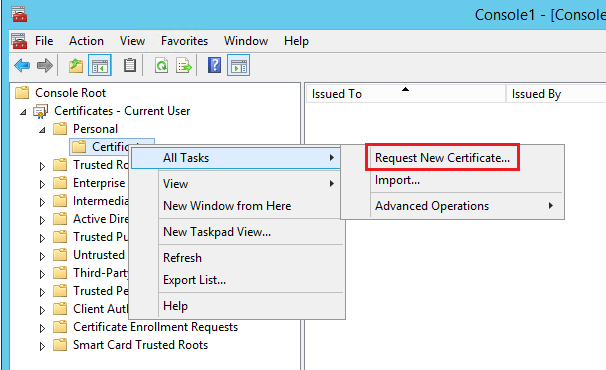
To sign a PowerShell Script, you must use a Code Signing Certificate. First, Open MMC and navigate to:
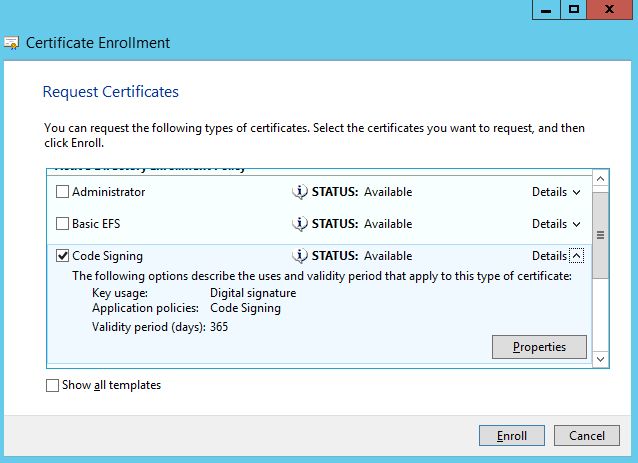
Right Click on Personal -> Certificates – > Request New Certificate
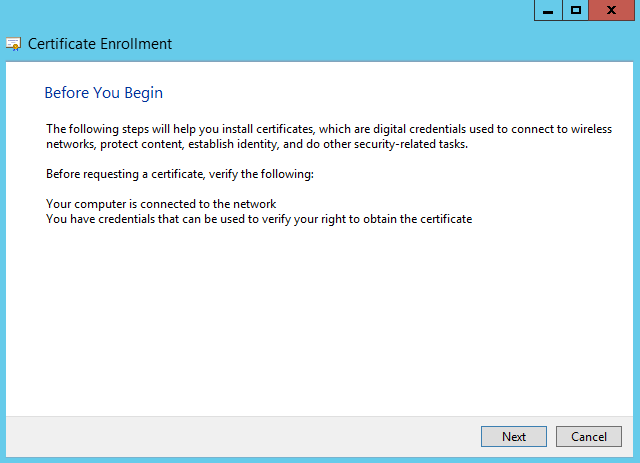
Click Next
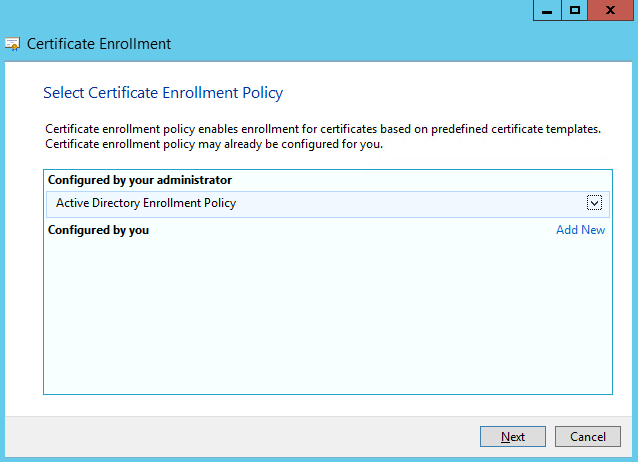
Click Next
Select “Code Signing” and select “Properties”
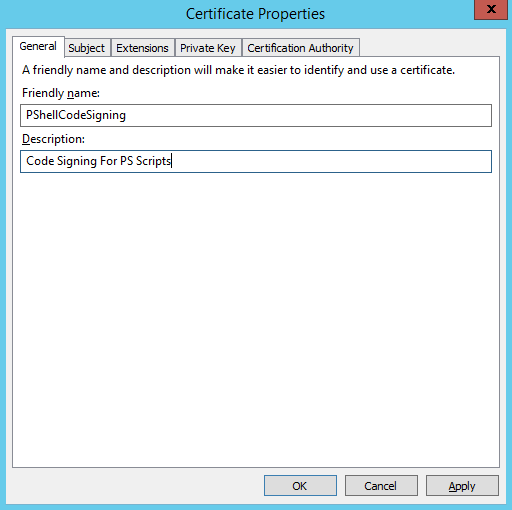
Type a Friendly Name
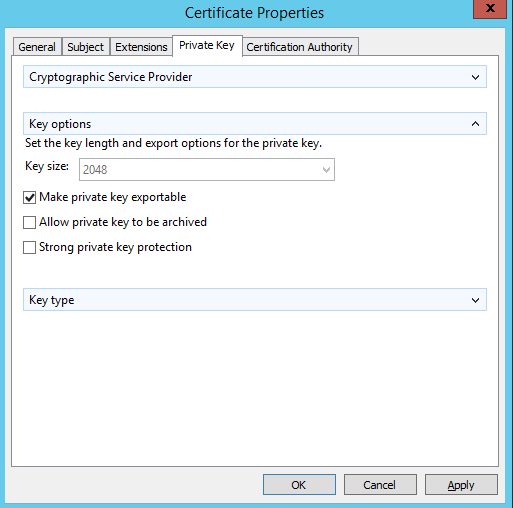
Select “Make private key exportable”
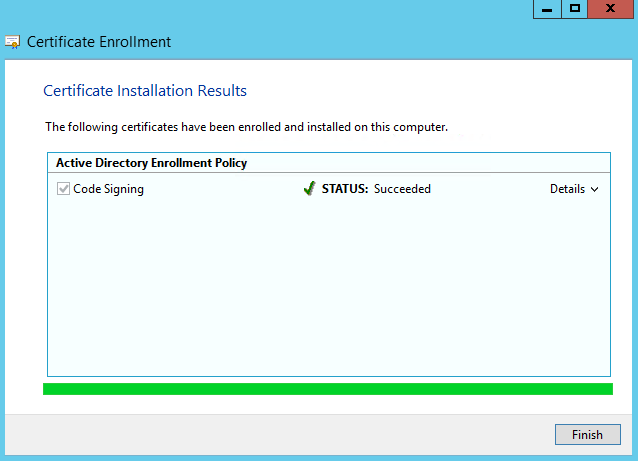
Click Enroll and Finish.
Now you can check the new certificate under personal store. All you need to do is to sign your PowerShell script with this certificate. The command used is Set-AuthenticodeSignature.
The certificate store is directly accessible as PSDrive, run the following commands:
PS> $MyCert =(dir Cert:\CurrentUser\My -CodeSigningCert)[0] PS> Set-AuthenticodeSignature .\YourPowerShellScript.ps1 -Certificate $MyCert
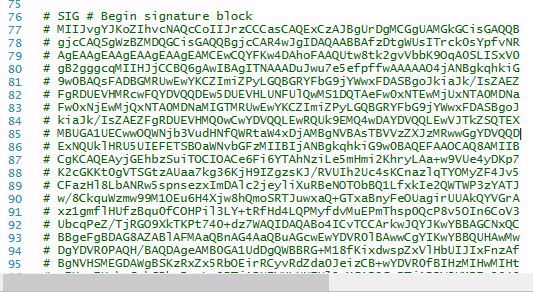
If you open your script, you will note that it now has a signature at the end of the script:
Thanks for reading! You can follow me on Twitter @PrigentNico